The 7 Most Common SaaS Architecture Mistakes (And How to Avoid Them)
Architecture decisions have a long half-life
A bad feature can be rewritten. A bad architecture is much harder to undo. The decisions you make about how to structure your SaaS product in the early weeks — how tenants are isolated, how the API is organised, how the database is modelled — will shape what is easy and what is painful for years.
We have seen these mistakes many times across the products we have taken over, audited, or helped rescue. Here are the seven that come up most often.
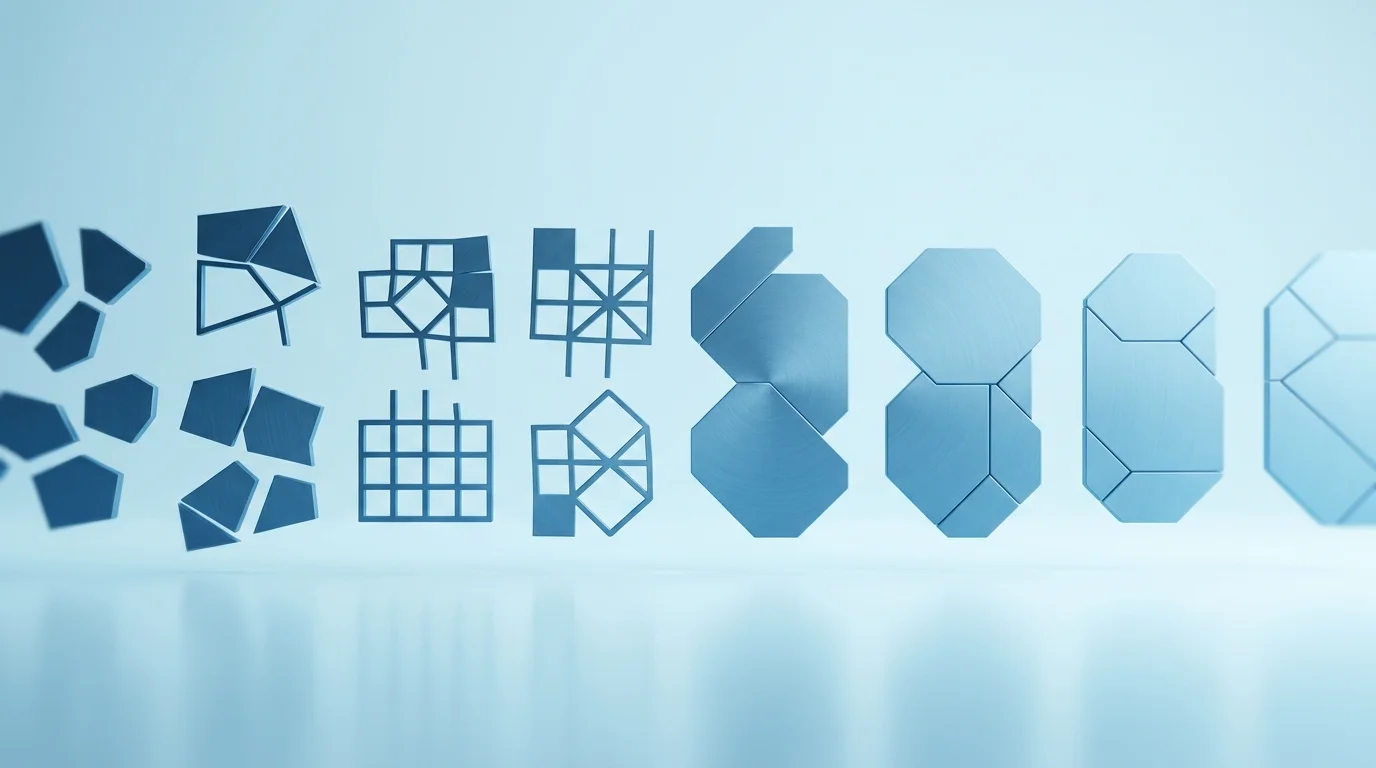
Mistake 1: Ignoring multi-tenancy until it's too late
Multi-tenancy — the ability for a single instance of your software to serve multiple customers with their data isolated from one another — is one of the defining characteristics of SaaS. But many early SaaS products are built without it in mind, essentially functioning as a single-tenant application that happens to have a login system.
The problem comes when you need to isolate data properly, add per-tenant configuration, or handle per-tenant billing. Retrofitting multi-tenancy onto an application that was not designed for it is an enormous amount of work — typically more than the original build.
What to do instead: Design multi-tenancy in from day one. This does not have to mean the most sophisticated implementation — schema-per-tenant, row-level security, or application-level filtering all have their place — but you need to pick an approach and be consistent with it from the start.
Mistake 2: Monolithic database design with no thought for scale
Relational databases are excellent, and for most SaaS applications a well-designed PostgreSQL database will take you further than you might expect. The problem is when the schema is designed without any thought for query patterns, indexing, or data volumes at scale.
The classic failure mode: a table with millions of rows and no indexes beyond the primary key. Queries that ran in milliseconds with a thousand rows take several seconds with a million. Your application slows to a crawl, and the fix requires downtime to add indexes or a painful migration to a different data model.
What to do instead: Think about query patterns as you design the schema, not after. Add indexes for the columns you know you will filter and sort by. Use database connection pooling from the start. Consider whether your read-heavy queries could benefit from caching before scaling the database itself.
Mistake 3: Coupling everything together in one codebase with no clear boundaries
A monolith is not inherently bad — in fact, for early-stage SaaS a monolith is usually the right choice. The problem is a monolith with no internal structure: where the authentication code directly calls the billing code which directly calls the email sending code, all tangled together in ways that make it impossible to change one thing without breaking several others.
What to do instead: Enforce module boundaries within your monolith. Group code by domain — billing, notifications, auth, core product — and ensure that domains communicate through defined interfaces rather than calling each other's internals directly. This gives you the simplicity of a monolith with the flexibility to extract services later if you genuinely need to.
Mistake 4: No background job infrastructure
SaaS products almost always need to do work that should not happen synchronously in a web request: sending emails, processing data imports, generating reports, syncing with third-party APIs, sending webhooks. Many early products handle these things in-process, which means they block web requests, fail silently when something goes wrong, and have no retry mechanism.
What to do instead: Set up a proper background job infrastructure from the start. Tools like Sidekiq (Ruby), Celery (Python), or BullMQ (Node.js) are well-established and easy to add early. You want visibility into what jobs are running, what has failed, and the ability to retry failures — not logs buried in your application output.
Mistake 5: Treating security as a feature to add later
Security is not a feature. It is a property of a system that requires intentional design from the beginning. The most common security mistakes in early SaaS products include: insufficient input validation, SQL injection vulnerabilities from string-interpolated queries, lack of rate limiting on authentication endpoints, poor secrets management (secrets in code, not environment variables), and missing or misconfigured CORS headers.
What to do instead: Follow OWASP's top ten as a checklist during development. Use parameterised queries — not string interpolation — for database access. Use a secrets manager for sensitive credentials. Implement rate limiting on any public-facing endpoint. Get an external security review before launch if you are handling sensitive data.
Mistake 6: No observability from day one
When something goes wrong in production — and it will — you need to be able to understand what happened. Without structured logging, error tracking, and application performance monitoring, you are blind. You will find out about problems from angry customers rather than from your own systems.
What to do instead: Set up error tracking (Sentry is excellent and has a free tier), structured logging, and basic application performance monitoring before you launch. These tools take hours to set up and save enormous amounts of time when diagnosing issues in production. Add alerting so you know about problems before your customers do.
Mistake 7: Ignoring the deployment and operations story until launch
Too many SaaS products reach launch day with no defined deployment process. Code gets pushed to production by one person, from their laptop, using a process that only they understand. There is no staging environment, no automated tests running before deployment, and no rollback plan.
What to do instead: Set up your CI/CD pipeline in week one. Every code change should go through automated tests before it can be deployed. Maintain a staging environment that mirrors production. Define and test your rollback procedure before you need it. None of this is glamorous, but all of it matters enormously once real customers are using your product.
The common thread
Every one of these mistakes shares the same root cause: treating the early build as a prototype rather than a foundation. The decisions you defer because they feel premature are exactly the ones that become expensive later.
The goal is not to over-engineer from the start. It is to make the right decisions — multi-tenancy, proper data modelling, good deployment practices — even when the product is small. These things are much cheaper to do right the first time than to fix under pressure at scale.
 Custom SaaS Development
Custom SaaS Development Technical Consulting
Technical Consulting